Transformation and Adoption… Be Cautious
2017 has been a transformative year for cybersecurity. We saw many organizations continue to adopt big data environments to store the immense amount of data that they have collected; and in doing so, we have been confronted with a new set of security challenges.
The past year certainly took us by surprise when the WannaCry and Petya ransomware outbreaks hit businesses globally, causing unprecedented disruption, while serious new vulnerabilities such as BlueBorne were discovered in almost every connected device in use.
Now, it’s 2018. Let us take a look into what are these emerging cyber-trends and what should we be prepared of in the future in terms of cybersecurity:
Ransomware
Ransomware is a problem on the rise, a simple threat that has huge implications. Statistics show it has reached new levels of menace, and it’s growing at a remarkable rate: 6000% in 2016, and a triple-digit increase into 2018.
Ransomware is a growing threat not only on laptops but also on mobile devices, which saw a 250% increase in infections, as well as smart devices. If you are connected to the internet, you are at risk, and any business or person is susceptible. Without proper back-ups and effective security measures in place, the risk of infection and success rates of ransomware will only continue to grow, thereby leaving us open to blackmail. The real question is how this threat is going to grow this year of 2018 and beyond.
Breaches Might Get Worse
After a year marked by devastating cyber attacks and breaches, online attackers are expected to become even more destructive in 2018. Ransomware outbreaks of 2017 offer just a taste of what’s to come as hackers develop new strategies in cyber attack.
The evolution of ransomware in 2017 should remind us of how aggressively a threat can reinvent itself as attackers dramatically innovate and adjust to the successful efforts of defenders. It is also predicted wider use of cyber attacks as a service in 2018 allowing more hackers for hire to have an impact.
 More Mobile Threats
More Mobile Threats
Mobile applications have been a target of choice for hackers to access and steal data, with 88% of mobile threats coming from them. Major apps suffered data breaches which resulted in the leakage of millions of users’ private data.
With smartphones becoming a part of our day to day lives, we end up doing all kinds of transactions and communications using them. This makes mobile security important, there are threats to mobile security that arise when people use their devices to connect to public Wi-Fi networks. Research and studies show that now mobile device users are getting more and more susceptible to phishing scams compared to those using desktops.
Thus, with mobile malware infections becoming a not-so-uncommon thing to major mobile security threats, we must be really cautious this 2018.
We’ll never know how, when and which variant might hit you but here’s how can you stay protected.
Network Security with SonicWall Firewalls.
SonicWall Firewalls.

The SonicWall Next Generation Firewalls are your first line of defense against Internet security threats and controlling data to the Internet. With its DPI-SSL (Deep Packet Inspection of Secure Sockets Layer), you would be able to gain visibility against encrypted traffic to stop threats.
Security 9.0, a cloud-based, multi-engine sandbox that does not only inspect email traffic for suspicious code, but also blocks malicious files from entering the network until a verdict is reached.
SonicWall also has the Capture Advanced Threat Protection Service which is a cloud-based multi-engine sandbox designed to discover and stop unknown, zero-day attacks such as ransomware at the gateway with automated remediation.
But is Network Protection enough? How about protecting your internal files?
File Protection with FinalCode.
Confidential files might be subjected to data leakage intentionally or unintentionally especially when you share them with extended parties and this is beyond your control. Have you been neglecting the need to secure these files? Or you never think it is possible?
FinalCode is an Information Rights Management Solution which allows you to have full control of your files in and out of your company’s network. You can control:
WHO can open your file
WHEN they can open your file
WHAT they can do with your file
You can even remotely delete your files once you detect an unauthorized access!
But cyber-attacks may not just be because of emails, encrypted traffic, or data leakage alone–it could also be behind the links while you surf the Web…
Web Protection with Menlo’s Isolation Platform.
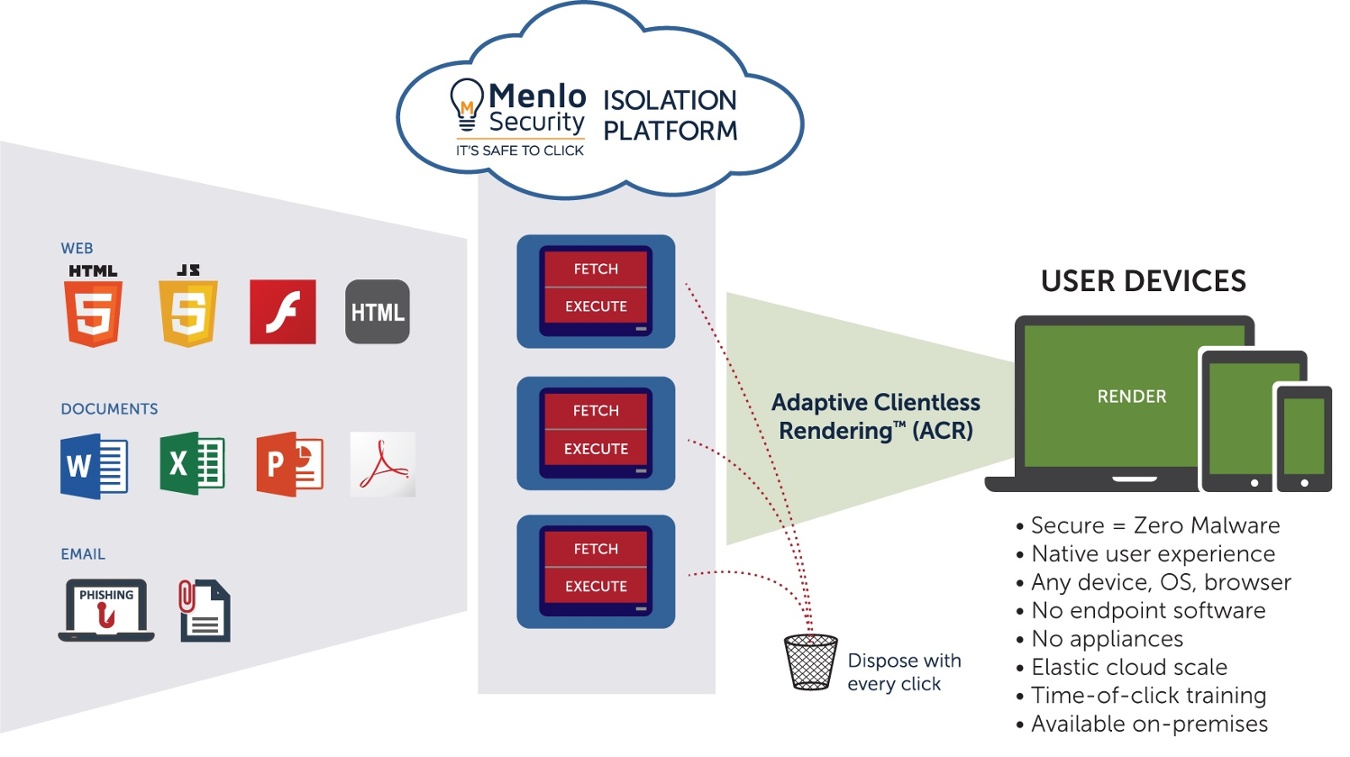
Menlo’s cloud-based isolation and Adaptive Clientless Rendering™ (ACR) technology, isolates a user’s session, meaning all content (e.g. Java, Flash etc.) is fully contained in the MSIP platform.
Only safe, malware-free rendering information is delivered to the user’s endpoint. Malware or ransomware has no path to reach an endpoint, meaning legitimate content needn’t be blocked by IT security. Administrators can open up more of the internet to their users while simultaneously eliminating the risk of attacks.
The Ultimate Attack Countermeasure: BACKUP
While Veeam® doesn’t prevent ransomware, the Veeam solution for ransomware following the 3-2-1 Rule of data protection along with advanced features native to the Veeam Availability Suite™ enables companies to quickly and effectively restore critical data infected by ransomware to a known good state:
In 2018, we might become even more reliant on and immersed in our hyper-connected world. Every network we use could be targeted wherever we’re connected, and the information we digest might be manipulated without us noticing it. Thus, we need to secure our networks and data better so that we can trust the services we use, and ensure the integrity of the data we produce and consume.
The future is coming, and we can’t see what it holds ahead of us – so this time, we need to be ready.
Follow us on Linkedin



 More Mobile Threats
More Mobile Threats
